Table of Contents
1. Why PCI DSS Exists
2. What Changed in PCI DSS 4.0
3. PCI DSS Merchant Levels
4. The 12 PCI DSS 4.0 Requirements
5. Step-by-Step Process to Become PCI DSS Compliant
6. Common PCI DSS Compliance Mistakes
7. Tools That Help With PCI DSS Compliance
8. PCI DSS Compliance Costs
9. Penalties for PCI DSS Non-Compliance
10. Conclusion
Why does PCI DSS Exist?
Card payments dominate modern commerce. The Federal Reserve System reports that payment cards account for over 70% of consumer transactions in the United States. This scale makes payment systems a prime target for cybercriminals.
Data breaches frequently expose financial information. The Identity Theft Resource Center recorded more than 3,200 data breaches in the U.S. during 2023, many involving sensitive financial records. Stolen payment data allows criminals to perform fraudulent transactions or sell card information on underground markets.
To reduce these risks, major card networks created the PCI Security Standards Council, which manages the Payment Card Industry Data Security Standard. The council was founded by Visa Inc., Mastercard, American Express, Discover Financial Services, and JCB Co., Ltd.
Who Needs PCI DSS Compliance? Organizations that handle payment cards must meet PCI DSS requirements, including:
* E-commerce platforms
* Payment processors and gateways
* SaaS platforms managing subscriptions
* Retailers using POS systems
* Service providers storing payment data
What Counts as Cardholder Data? PCI DSS protects the Primary Account Number (PAN) and related information, such as:
* Cardholder name
* Expiration date
* Service code
Systems Within PCI Scope
* The standard covers the cardholder data environment, which includes:
* Payment gateways
* POS systems
* Databases storing payment data
* Web and application servers processing transactions
For Example, A simplified PCI-compliant architecture might look like this:
1. A customer enters payment details on an e-commerce checkout page
2. The web application sends the payment request to a payment gateway.
3. The gateway communicates with card networks and issuing banks to approve the transaction
4. Sensitive card data is encrypted and stored only within the secure CDE database
5. Logging systems record transaction activity for monitoring and compliance
In this model, only the payment application, gateway integration, and protected database fall inside the CDE, while the rest of the business infrastructure remains outside the compliance scope.
What Changed in PCI DSS 4.0
PCI DSS 4.0 Update: The PCI DSS 4.0 update was released in March 2022 by the PCI Security Standards Council with 60 new or updated security requirements, with full enforcement beginning March 31, 2025, to address modern payment security threats and new technologies such as cloud infrastructure and e-commerce payment platforms.
The new version updates several controls to protect cardholder data in cloud platforms, e-commerce environments, and distributed payment systems. Below are the major changes organizations must implement:
- Stronger authentication controls: Organizations must implement stronger identity verification to prevent unauthorized access to systems that handle cardholder data. This includes wider adoption of multi-factor authentication and stricter credential management.
- Continuous Monitoring: The updates standard emphasizes continuous visibility into payment environments. Organizations must improve logging, monitoring, and alerting so security teams can detect suspicious activity quickly.
- Modern Payment Environments: Payment infrastructure now includes APIs, distributed applications, and cloud-based services. PCI DSS 4.0 introduces guidance to secure these modern architectures.
- Cloud infrastructure responsibility: Organizations that rely on cloud providers must clearly define which security responsibilities belong to the organization and which belong to the provider. This helps ensure cardholder data remains protected in shared infrastructure.
- Client-side ecommerce security: Many recent breaches involve malicious scripts injected into checkout pages. PCI DSS 4.0 introduces controls requiring businesses to monitor scripts running on payment pages and verify their integrity.
PCI DSS 4.0 Compliance Timeline
Organizations must follow a defined transition timeline.
* March 2022: PCI DSS 4.0 officially released
* March 31, 2024: The Previous version of PCI DSS 3.2.1 retires
* March 31, 2025: All future-dated PCI DSS 4.0 requirements become mandatory.
PCI DSS Merchant Levels
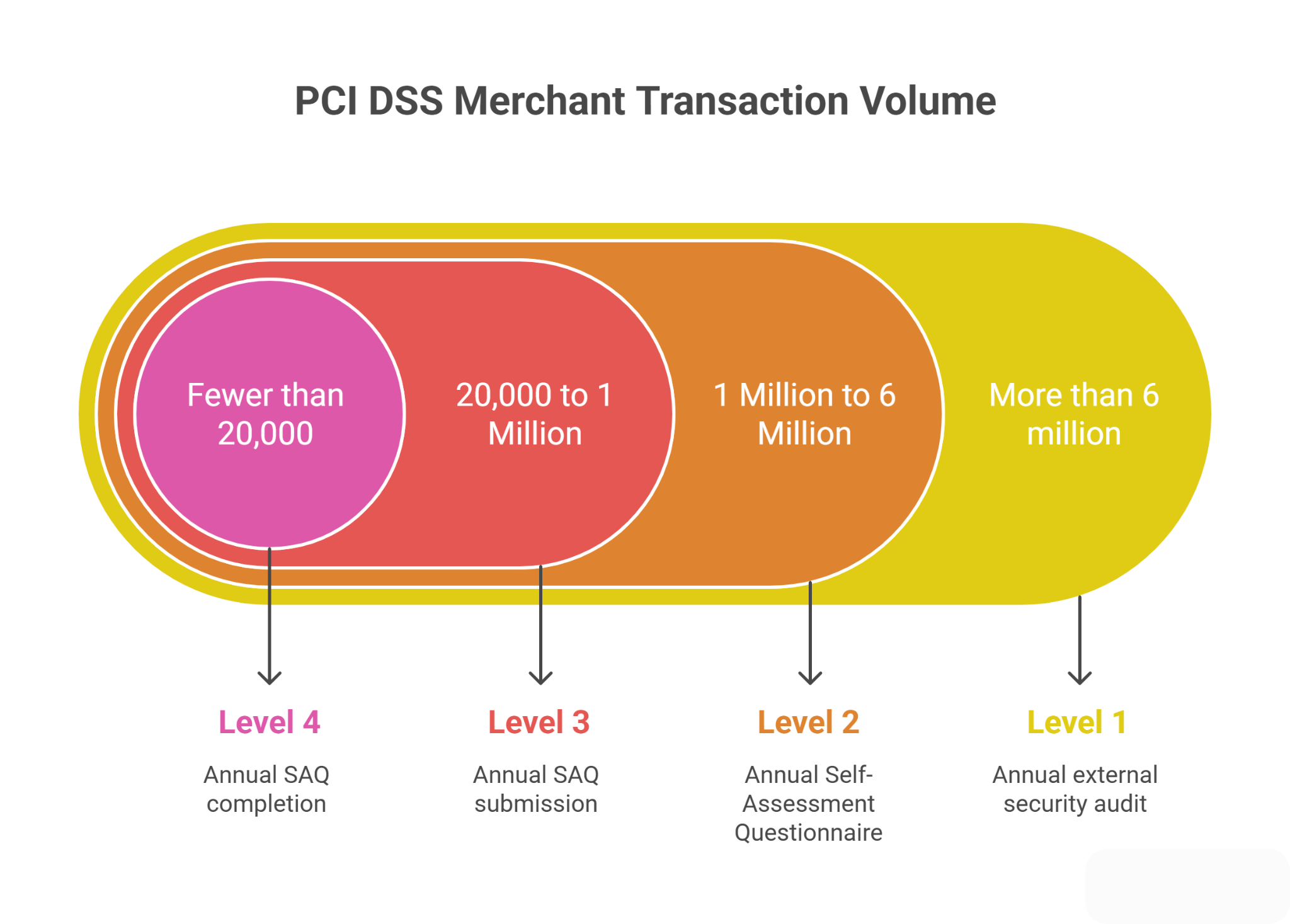
Payment brands classify merchants into four PCI DSS levels based on the number of payment card transactions processed each year. The level determines the type of validation and security assessment required to confirm compliance.
Level 1: More than 6 million transactions per year
Large merchants processing high transaction volumes fall into Level 1. These organizations must complete the most rigorous validation process.
Validation Requirements
* Annual external security audit conducted by a Qualified Security Assessor (QSA)
* Report on Compliance (ROC) documenting how PCI DSS controls are implemented.
* Quarterly external vulnerability scans performed by an Approved Scanning Vendor (ASV)
Level 2: 1 Million to 6 Million Transactions per year
Mid-size merchants must validate compliance through structured internal assessments.
Valid Requirements
* Annual Self-Assessment Questionnaire (SAQ)
* Quarterly external vulnerability scans by an ASV
Level 3: 20,000 to 1 Million ecommerce transactions per year
Online merchants with moderate transaction volume fall into this category.
Valid Requirements
* Annual SAQ submission
* Quarterly vulnerability scans
Level 4: Fewer than 20,000 ecommerce transactions per year or under 1 million total card transactions
Small merchants still must maintain PCI security controls, but follow a simpler validation process.
Validation requirements
* Annual SAQ completion
* Basic security checks and recommended vulnerability scans
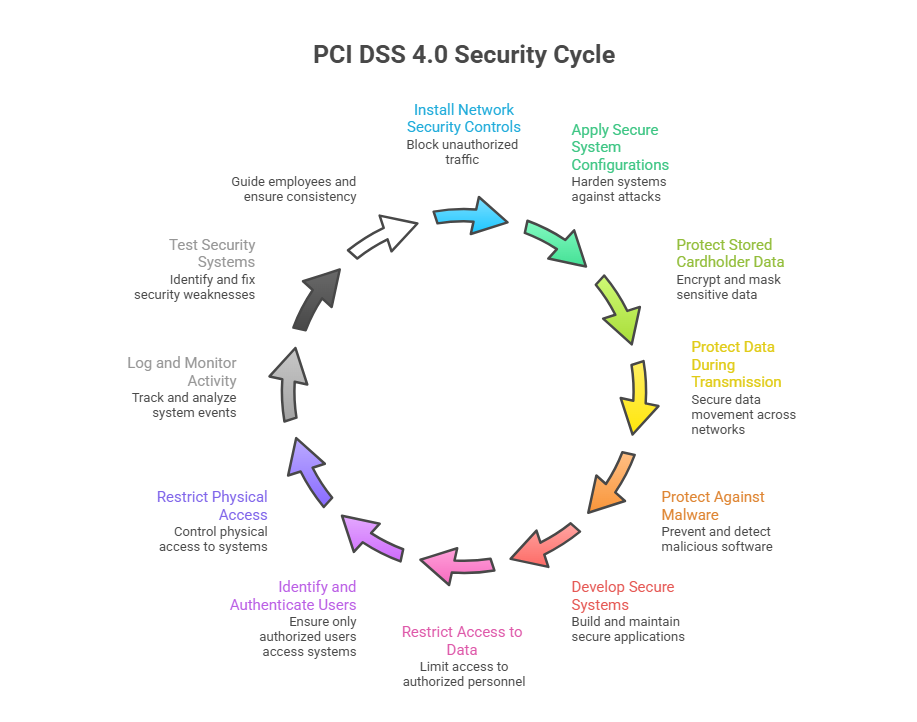
The 12 PCI DSS 4.0 Requirements
Organizations that accept credit card payments must follow the framework defined by PCI DSS 4.0. Each requirement protects cardholder data from unauthorized access, theft, or misuse. The sections below explain what each requirement means and how organizations apply it in practice.
Requirement 1: Install and Maintain Network Security Controls
Network security controls block unauthorized traffic from entering systems that store or process cardholder data.
Implementation Steps
* Configure firewalls and network security controls
* Segment payment environments from other business networks
* Define allowed inbound and outbound traffic rules
* Deploy intrusion detection or intrusion prevention systems
* Restrict direct internet access to payment servers
Compliance Checklist
* Firewall rules are reviewed every six months
* Documented network security policies
* Unauthorized network connection blocked
* Network segmentation controls are tested regularly
Requirement 2: Apply Secure System Configurations
Default System Settings create Easy Points for Attackers
Implementation Steps
* Change vendor default passwords immediately
* Disable unnecessary services and open ports
* Apply system hardening standards across servers and devices
* Remove sample files, test, accounts, and unused applications
Compliance Checklist
* Secure router and switch configurations
* Password management policies are in place
* Documented configuration baselines are maintained
* Administrative interfaces are rarely restricted to trusted networks
Requirement 3: Protect Stored Cardholder Data
Stored payment information becomes a high-value target during breaches.
Implementation steps
* Encrypt stored card numbers
* Mask the primary account number when displayed
* Remove card data because that is not required
* Implement tokenization for stored cardholder data
* Secure encryption keys using hardware security modules or key management systems
Compliance Checklist
* Strong encryption, such as AES-256
* Tokenization where possible
* Defined data retention policies
* Secure encryption key management procedures
Requirement 4: Protect Cardholder Data During Transmission
Attackers may intercept payment data while it moves across networks.
Implementation steps
* Encrypt all transmissions of cardholder data
* Use secure communication protocols
* Secure integrations and payment APIs
* Prevent transmission of card data over insecure channels
* Secure internal network communications between payment systems
Compliance checklist
* TLS 1.2 or higher enforced
* Insecure protocols disabled
* Secure API communication
* Payment forms are protected using HTTPS
Requirement 5: Protect Systems Against Malware
Malware can capture payment data or compromise payment systems.
Implementation steps
* Install anti-malware software on all relevant systems
* Monitor endpoints handling payment data
* Enable automatic malware detection
* Deploy endpoint protection platforms for threat detection
* Restrict users' ability to install unauthorized software
Compliance checklist
* Automatic signature updates
* Scheduled malware scans
* Central monitoring of malware alerts
* Anti-malware protection is active on all relevant systems
Requirement 6: Develop and Maintain Secure Systems and Applications
Software vulnerabilities expose payment systems to attacks.
Implementation steps
* Maintain a patch management program
* Identify and fix security vulnerabilities
* Follow secure software development practices
* Monitor third-party libraries and dependencies for vulnerabilities.
* Validate application security before production deployment
Compliance checklist
* Critical patches applied within 30 days
* Code security reviews performed
* Third-party software monitored
* Software update tracking documented
Requirement 7: Restrict Access to Cardholder Data
Only authorized staff should access sensitive payment information
Implementation steps
* Apply role-based access control
* Grant minimum access needed to perform tasks
* Implement access approval workflows
* Monitor administrative and privileged user activity
* Restrict database access to authorized services and users
Compliance Checklist
* Quarterly access reviews
* Removal of inactive accounts
* Monitoring of privileged access
Requirement 8: Identify and Authenticate Users
Strong authentication prevents unauthorized users from entering systems.
Implementation steps
* Assign unique user IDs to each individual
* Lock accounts after repeated failed login attempts
* Secure authentication mechanisms for remote access
* Implement strong authentication controls
Compliance checklist
* Multi-factor authentication for administrators
* Password rotation policies
* Login activity monitoring
Requirement 9: Restrict Physical Access to Cardholder Data
Physical access to systems may allow attackers to steal data or install malicious devices.
Implementation steps
* Control entry to server rooms and data centers
* Secure payment terminals and storage devices
* Implement access badges or biometric entry systems
* Protect backup media and removable storage devices
* Inspect payment terminals for tampering
Compliance checklist
* Visitor access logs
* Surveillance systems in secure areas
* Device inventory tracking
Requirement 10: Log and Monitor System Activity
Security logs help teams detect suspicious activity and investigate incidents.
Implementation steps
* Enable logging across payment systems
* Monitor logs for unusual behaviour
* Monitor administrative and user activity
* Generate alerts for suspicious login attempts or system changes
* Protect log files from modification or deletion
Compliance checklist
* Centralized log management system
* Log retention for at least one year
* Daily log review procedures
* Security alerts configured for critical events
Requirement 11: Test Security Systems Regularly
Security testing identifies weaknesses before attackers find them
Implementation steps
* Perform vulnerability scans
* Conduct penetration testing
* Evaluate wireless network security
* Validate intrusion detection and alerting systems
Compliance checklist
* Quarterly vulnerability scans
* Annual penetration testing
* Wireless security scans
Requirement 12: Maintain Security Policies and Governance
Strong security policies guide employees and maintain consistent protection practices.
Implementation steps
* Create documented security policies
* Train employees on data protection
* Manage risks from third-party vendors
* Establish vendor security evaluation processes
* Maintain an incident response plan for security breaches
Compliance checklist
* Incident response plan
* Employee security training program
* Vendor security management procedures
* Security policies are reviewed and updated regularly.
Step-by-Step Process to Become PCI DSS Compliant
Achieving compliance with PCI DSS 4.0 requires a structured process: identify payment data, secure the environment, test controls, and validate compliance.
Step 1: Identify Systems Handling Card Data
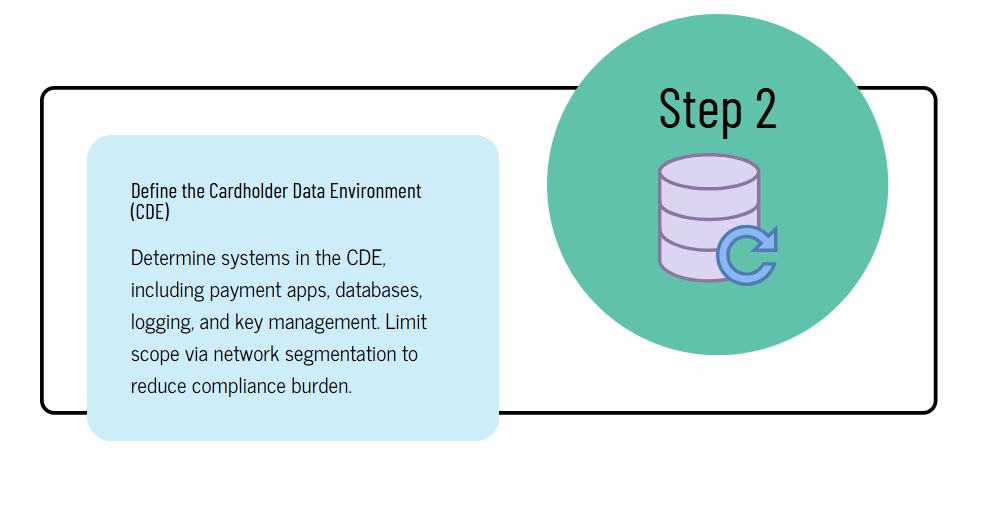
Step 2: Define the Cardholder Data Environment (CDE)
Step 3: Perform a PCI Gap Assessment
Step 4: Implement Required Security Controls
Step 5: Perform Vulnerability Scans
Step 6: Conduct Penetration Testing
Step 7: Complete Compliance Validation
Step 8: Submit Compliance Documentation
Common PCI DSS Compliance Mistakes
Many organizations fail PCI DSS audits due to preventable mistakes. These gaps increase the risk of payment fraud, data breaches, and regulatory penalties.
1. Strong Card Data Without a Business Need
Some companies keep full card numbers in databases or logs even when payment processing is complete. PCI DSS allows storage only when it is absolutely required. Unnecessary storage increases the damage a breach can cause. Attackers target databases that contain full cardholder records.
2. Missing Network Segmentation
A poorly segmented network places the Cardholder Data Environment (CDE) inside the same network as office systems, email servers, or employee laptops.
Without segmentation:
* Attackers who compromise a single workstation may reach payment systems
* The PCI scope expands across the entire network
* Security monitoring becomes harder
Segmentation limits access to systems that process payments.
3. Weak Encryption of Cardholder Data
PCI DSS requires strong encryption for stored and transmitted card data. Common mistakes include:
* Outdated encryption algorithms
* Poorly managed encryption keys
* Storing unencrypted card numbers in backups or logs
Weak encryption exposes card data if attackers gain database access.
4. Poor Logging and Monitoring
Many companies collect logs but never review them. Effective monitoring requires:
* Centralized logging
* Daily log review procedures
* Alerts for suspicious activity
Without monitoring, attackers can remain inside systems for months without detection.
5. Ignoring Patch Management
Outdated software remains one of the easiest ways attackers gain access to payment systems. Common problems include:
* Delayed Operating system updates
* Unpatched web servers
* Outdated e-commerce platforms
PCI DSS requires regular vulnerability scans and prompt patch deployment to reduce exposure.
PCI DSS v4.0 Deadlines: Everything You Need to Know
Tools That Help With PCI DSS Compliance
Security teams rely on specialized tools to monitor systems, detect threats, and validate compliance. These technologies support several PCI DSS requirements.
1. SIEM Platforms
Security Information and Event Management tools collect and analyze logs from across the payment environment. Popular platforms include Splunk, IBM QRader, and Microsoft Sentinel.
2. Vulnerability Scanners
These tools identify security weaknesses in servers, applications, and network devices. Common solutions include Tenable Nessus, Qualys Vulnerability Management, Rapid7 InsightVM
3. Log Management Systems
Log management platforms store and organize system logs required for PCI audits. Examples include Elastic Stack and Graylog.
4. Tokenization Solutions
Tokenization replaces sensitive card numbers with random tokens. The real card data stays inside a secure vault. Common providers include Stripe and Adyen.
5. Endpoint Security Platforms
Endpoint protection tools secure servers and employee devices that access payment systems. Famous platforms include CrowdStrike Falcon and Microsoft Defender for Endpoint.
These platforms detect malware, suspicious processes, and unauthorized system activity.
PCI DSS Compliance Costs
PCI DSS 4.0 implementation costs depend on how many systems handle payment data and how large the Cardholder Data Environment (CDE) is. A small online store may spend a few thousand dollars. A large company with many payment systems may invest much more.
1. Infrastructure upgrades
Many organizations must adjust their payment architecture. Common upgrades include:
* Network segmentation to isolate the CDE
* Modern firewalls and secure gateways
* Encrypted databases for cardholder data
* Hardened servers and secure payment apps
2. Security technologies
PCI environments require several security tools:
* Web Application Firewall (WAF) for checkout protection
* Intrusion detection or prevention systems
* Centralized log monitoring platforms
* File integrity monitoring tools
3. Secure Testing
PCI rules require regular testing:
* Quarterly external scans by an Approved Scanning Vendor
* Annual penetration testing
* Internal vulnerability assessments
4. Compliance audits
Large merchants must undergo a formal audit performed by a Qualified Security Assessor.
|
Organization Type |
Estimated Cost |
|
Small ecommerce businesses |
$5,000- $20,000 |
|
Mid-size companies |
$20,000- $100,000 |
|
Large enterprises |
$100,000+ |
Initial setup tends to cost the most because companies redesign networks and deploy security monitoring systems.
Penalties for PCI DSS Non-Compliance
Failure to meet PCI DSS requirements can trigger fines, higher transaction fees, or loss of card payment privileges.
Financial Penalties
Major payment networks such as Visa Inc. and Mastercard can fine acquiring banks when merchants fail to meet security rules. Banks then pass those fines to the merchant.
PCI DSS Non-Compliance Penalties can range from $5,000- $100,000 per month until compliance is restored.
Operational Consequences
Non-compliant businesses may face:
* Higher credit card processing fees
* Mandatory forensic investigations after breaches
* Legal liability for stolen card data
* Suspension or termination of merchant accounts
A payment breach tied to poor security controls can also lead to millions of dollars in investigation and recovery costs.
Why PCI DSS Compliance Is Important for Every Business Accepting Card Payments
Final Thoughts
Payment card security affects every company that accepts or processes card payments. PCI DSS 4.0 sets updated expectations for protecting cardholder data, controlling access, monitoring systems, and responding to threats. Organizations that store, process, or transmit card data must review their systems, document controls, and validate compliance at the correct merchant level.
Smaller merchants usually complete a Self-Assessment Questionnaire (SAQ), while higher-volume merchants complete formal security audits and produce a Report on Compliance (ROC). Strong network segmentation, encryption, centralized logging, and multi-factor authentication reduce risk and support compliance requirements. Regular vulnerability scans and incident response testing keep security controls active.
PCI DSS should operate as an ongoing security practice rather than a one-time checklist. When companies map cardholder data, review access controls, and maintain continuous monitoring, they lower fraud risk and strengthen trust with customers, banks, and payment partners. Starting with clear data visibility and closing control gaps builds a stronger payment security foundation.

